Nitrogen Ransomware, Foxconn, and the Identity Architecture Problem Reshaping Enterprise Security
The Foxconn incident tied to the Nitrogen ransomware group is instructive — not because it reveals new attack techniques, but because it confirms a structural shift in how enterprise environments are compromised. Attackers are no longer primarily exploiting unpatched software. They are compromising identity systems, inheriting trusted sessions, and moving laterally through legitimate administrative pathways.
This is not an emerging trend. It is the established model.
Nitrogen campaigns, observed consistently since mid-2023, typically begin with malvertising operations targeting IT administrators and infrastructure engineers. Attackers purchase sponsored search advertisements impersonating legitimate enterprise tools — AnyDesk, Cisco AnyConnect, WinSCP, PuTTY, FileZilla — and redirect victims to cloned vendor sites serving trojanized installers. The initial access phase requires relatively little technical sophistication. The attack succeeds because the workflow appears entirely normal: the victim expects to download infrastructure software as part of routine operations.
Once executed, the Nitrogen payload chain uses DLL sideloading, Python-based staged loaders, PowerShell execution, and post-exploitation tooling including Cobalt Strike beacons. But code execution is not the primary objective. The objective is identity.
The attacker's goal is not malware persistence. It is to inherit the authentication trust already established on the compromised endpoint.
Why Privileged Endpoints Concentrate Risk
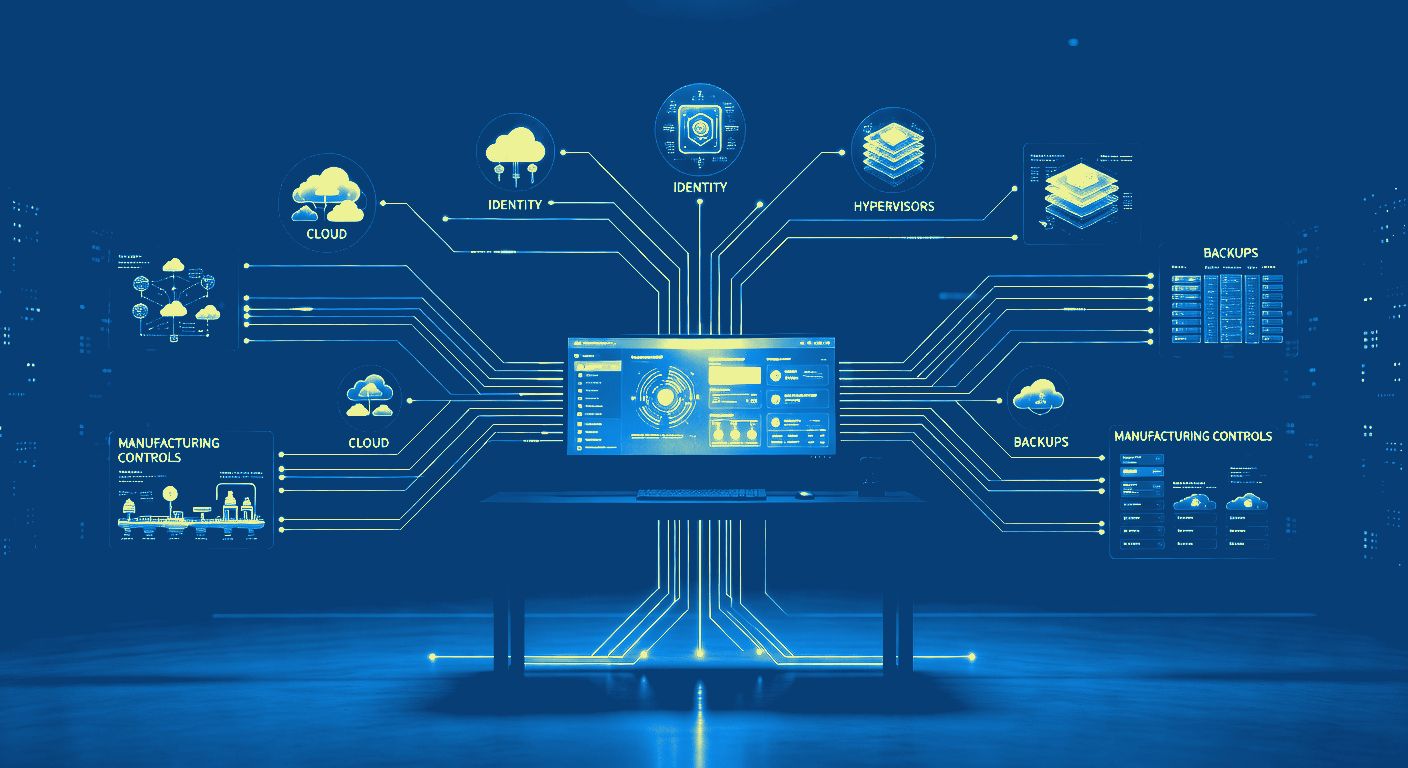
Modern enterprise infrastructure concentrates substantial authentication trust in privileged administrative endpoints. A single compromised IT workstation may hold active VPN sessions, federated SSO access, administrative browser sessions, cloud management interfaces, RDP trust relationships, virtualization infrastructure access, backup system credentials, and privileged identity provider sessions — simultaneously.
In many environments, multifactor authentication has already completed before the attacker arrives. The attacker does not bypass MFA. The attacker inherits the post-authentication state the legitimate user already established.
This is why ransomware operators target administrators over ordinary users. The ratio between one compromised privileged identity and downstream infrastructure exposure is asymmetric by design. A single endpoint can provide administrative pathways into hypervisors, identity providers, manufacturing systems, cloud control planes, and enterprise storage infrastructure at once.
The Foxconn incident reflects precisely this model. Once privileged access is established, blast radius expands rapidly — because traditional identity systems were built around reusable trust. Session persistence, bearer tokens, cached credentials, VPN artifacts, browser cookies, and federated SSO assertions all become mechanisms for lateral expansion.
Traditional MFA does not prevent this. It was not designed to address a compromised endpoint. It was designed to protect authentication at the perimeter — and that boundary no longer holds.
The Architectural Problem: Reusable Authentication State
Authentication systems based on SMS codes, push notifications, TOTP, and session approvals share a common structural limitation: they generate transferable authentication artifacts. They assume the endpoint remains trustworthy after authentication completes. Nitrogen-style operations consistently demonstrate that this assumption does not hold.
The problem is not credential theft in isolation. The deeper problem is reusable authentication state — the condition where one successful endpoint compromise becomes a persistent, expandable access hub across the broader environment.
Addressing this requires a different architectural foundation: one where authentication trust cannot be exported, replayed, or inherited from a compromised endpoint.
How Hardware-Bound FIDO2 Authentication Constrains Blast Radius
FIDO2/WebAuthn authentication architectures — specifically implementations combining hardware-isolated key storage, origin validation, biometric user verification, and proximity enforcement — address the identity amplification problem directly.
The relevant security property is not passwordless access. It is the elimination of reusable authentication state after compromise.
Four specific mechanisms define this protection:
- Origin binding. During registration, the authenticator associates a key pair with a specific relying party identifier — vpn.company.com, sso.company.com, admin.aws.company.com. During authentication, the browser supplies the RP ID hash for the requesting domain. The authenticator validates the match before signing. If the domain does not match the original registration context, the authenticator refuses. No push notification to approve. No code to relay. No user decision that can override the mismatch.
- Hardware-isolated key storage. The private signing key is generated and held within the authenticator's secure element. It never becomes accessible to the operating system, browser memory, or any process on the endpoint. Post-exploitation frameworks that target cached credentials, bearer tokens, and federated session artifacts cannot extract what never leaves the hardware.
- Biometric user verification. Authentication requires local biometric confirmation directly on the authenticator before any signing operation occurs. The biometric template remains isolated inside the authenticator hardware — it is never transmitted or centrally stored. Phishing, session interception, and coercion cannot substitute for the biometric presence of the verified individual.
- Proximity enforcement. Physical proximity requirements prevent attackers from remotely reusing authentication state from their own infrastructure after initial compromise. Remote administrative pivot operations depend on the ability to replay or delegate existing credentials. Proximity enforcement removes that capability.
The Right Question for Enterprise Security Leaders
No security architecture eliminates endpoint compromise. Malware executes. Privileged workstations are exposed. In sufficiently large environments, some proportion of these events will occur.
The determinative question is what happens next.
Nitrogen and Foxconn are case studies not in novel malware, but in identity amplification — the condition where one compromised endpoint cascades into environment-wide access because authentication trust was designed to persist and propagate.
Token Ring addresses this at the architectural level: hardware-bound cryptographic identity, FIDO2-certified origin validation, biometric-assured user verification, and proximity-aware authentication enforcement. Together, these properties reduce the blast radius of endpoint compromise by eliminating the reusable authentication state that ransomware operators depend on.
The question is not whether an endpoint will be compromised. The question is how much trust survives when it is. That answer now determines enterprise blast radius.
For CISOs making authentication architecture decisions, this is the correct frame. Perimeter defenses and endpoint detection address part of the problem. Identity architecture — specifically, whether authentication trust can be inherited, replayed, or delegated after compromise — determines the rest.


