The Biometric Authentication Device That Stops Ransomware
The only biometric-enforced, cryptographic identity wearable that verifies the human behind every login in real-time. Enterprise-grade security for every employee.
FIDO2 Certified
Wireless
No Passwords
No Codes
No PIN fallback
The problem isn’t access, it’s identity.
MFA is not enough. Most breaches start with a verified identity that should never have gained access.

Stolen credentials are the #1 access vector in enterprise breaches
The Verizon 2025 DBIR
Identity-based intrusions account for 30% of all incidents
IBM X-Force Threat Intelligence Index 2025
Absolute identity wherever your workstation is
Portable biometric authenticator built to defeat credential theft, phishing, and session hijacking at the source. When individual identity fails, everything fails.
Presence Detected:
Bluetooth proximity (3ft) confirms you are physically there.
Identity verified:
Your fingerprint unlocks the device (EAL5+) locally, on-device.
Cryptography executed:
A domain-bound credential is generated and signed ES256 elliptical curve cryptography.
No code, push notification, USB or friction to intercept
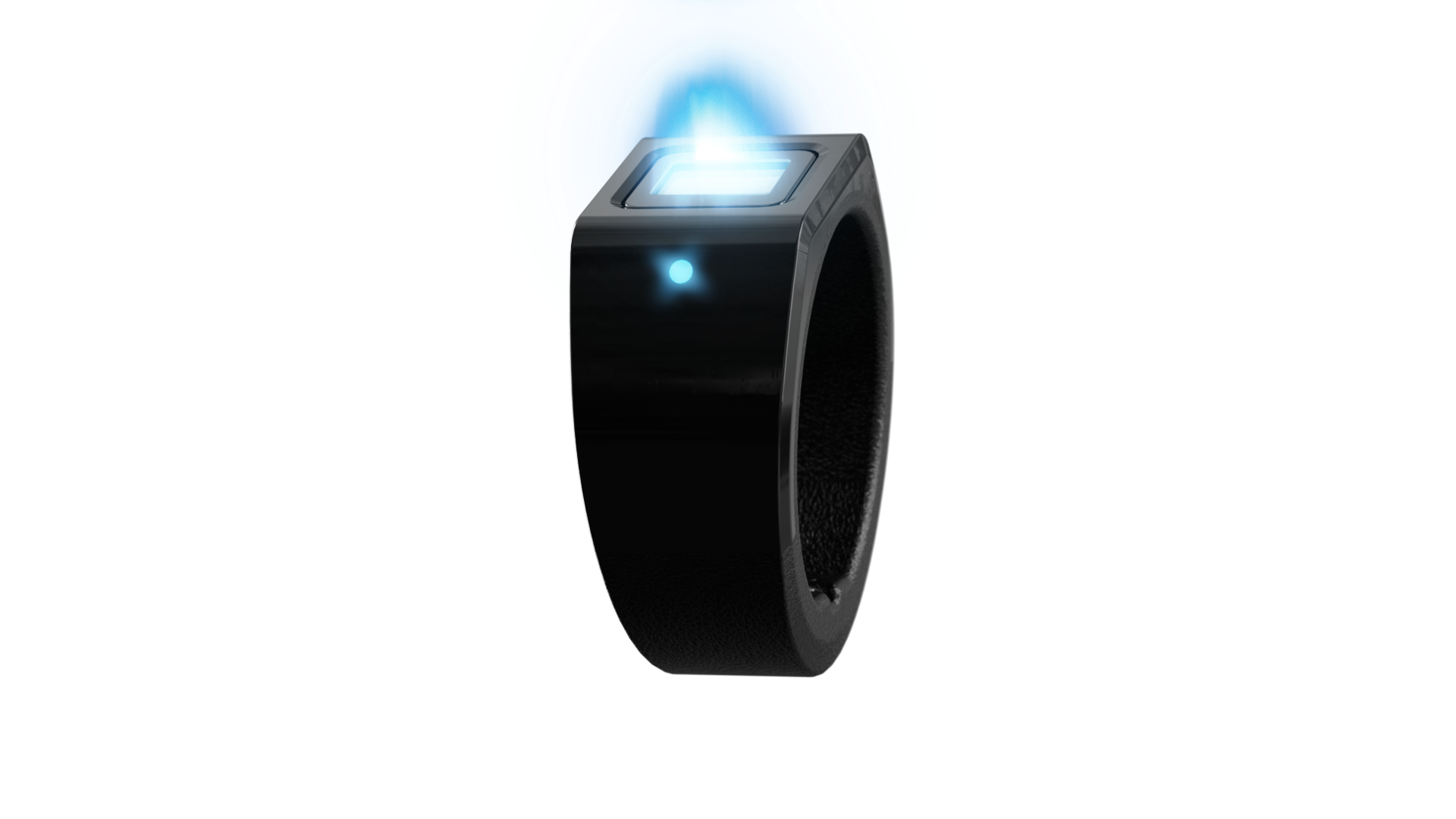
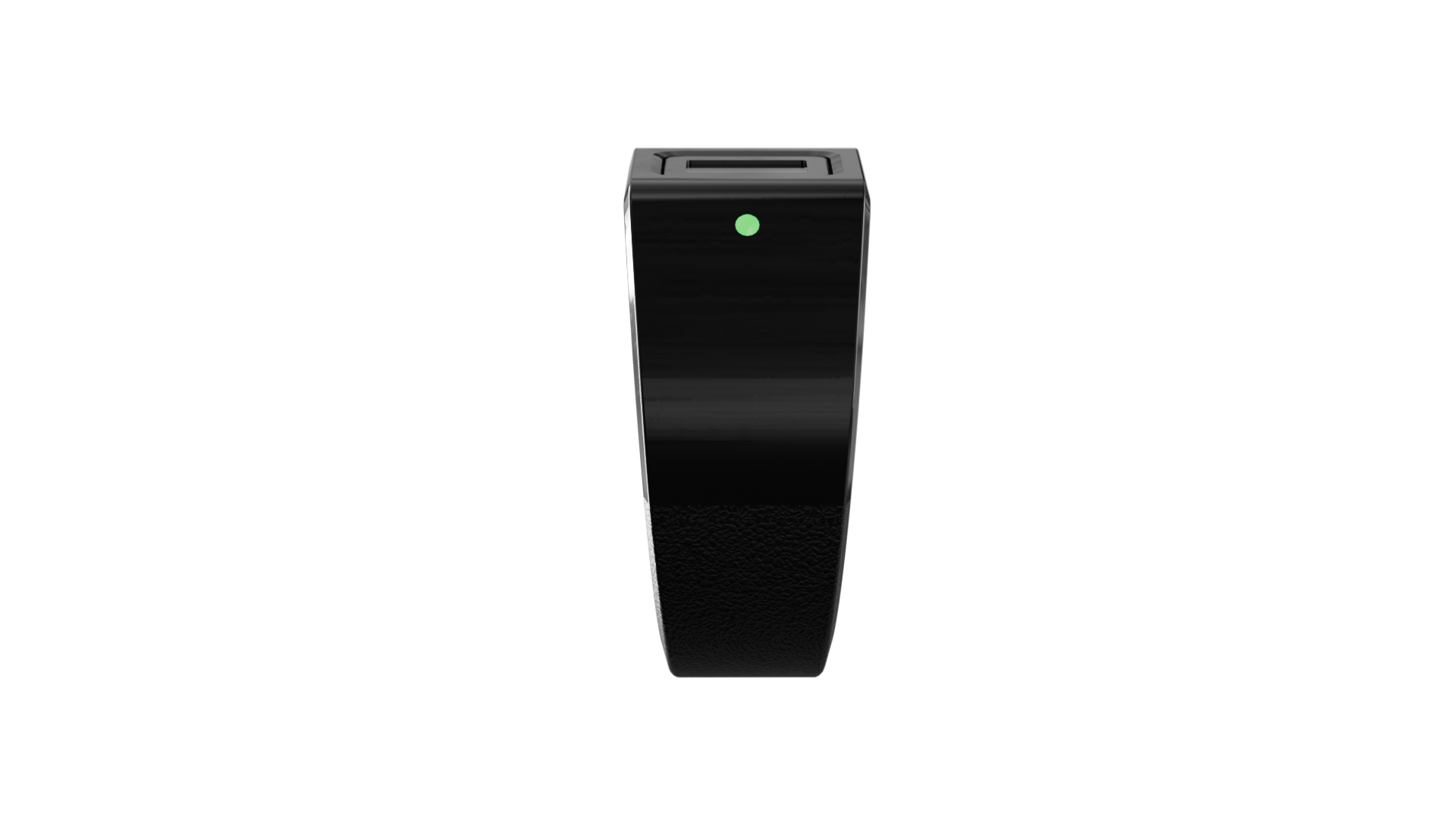
TokenCore™ Wearable
FIDO2 • Biometric • Passwordless

Presence Detected:
Bluetooth proximity (3ft) confirms you are physically there.
Identity verified:
Your fingerprint unlocks the device (EAL5+) locally, on-device.
Cryptography executed:
A domain-bound credential is generated and signed ES256 elliptical curve cryptography.
No code, push notification, USB or friction to intercept
TokenCore™ Wearable
FIDO2 • Biometric • Passwordless
Why TokenCore™ Wearable?

Wireless by Design
Authentication that moves with you. BLE 5.4 and encrypted NFC eliminate USB friction. Works across iOS, Android, Windows, and macOS without drivers, or middleware.

Proximity-Based Login
The wearable ensures authentication only occurs when it is near the intended device, preventing man-in-the-middle attacks and enhancing security.

Passwordless Authentication
The gesture feature allows the user to authenticate only when they intend to.

Upgradeable Firmware
A future-proof design ensures the Device can be optimized for performance and new capabilities in a flash with over-the-air firmware updates. No one else can do this.

Biometric Authentication
The FIDO2-compliant capacitive fingerprint sensor in TokenCore™ Wearable ensures only the user’s fingerprint will activate it, meaning no one else can.

Innovative Wearable
The ring is always with the user, so it is always safe and immediately available.

Secure Credentials
User credentials are stored on TokenCore™ Wearable, EAL5+ certified secure element for high security. No PIN bypass, without your fingerprint, no access.

Fully Interoperable
The Ring is fully compatible and can be deployed seamlessly with all leading IAM platforms within hours.
Zero Doubt

Operational in 30 Days
Integrates with Okta, Entra, Ping
Works with the identity stack you already trust.
No middleware required
Deploy without adding another layer to manage.
Pilot, initial rollout, without replacing your existing stack
Start fast without ripping out what already works.
Lock threat actors out altogether
- Reduce HelpDesk Costs
- Reduce Password Resets / Fatigue
- Reduce Insurance Premiums
TokenCore™ Wearable
Ring form factor stays with the user, increasing secure-use consistency across the workday. Supports frictionless biometric login with proximity-aware access over NFC/Bluetooth.
| Battery Life: | 5–7 days |
| Charge: | 90 minutes (fully charged) |
| Secure Element: | EAL5+ |
| Keys: | 100 FIDO credentials |
| Connectivity: | BLE 5.4 + NFC |
| Compatibility: | iOS, Android, Windows, macOS |
| Durability: | IP67 |
| Secure: | FIDO2 / WebAuthn |
Move Beyond Legacy MFA
For organizations identity needs to be absolute
From trading floors to intensive care units, TokenCore™ is designed for environments where failure is not an option.

Common Questions
Everything you need to know.
Identity Assurance is a new category. These are the questions we hear most — answered directly.
Yes, TokenCore™ Wearable is FIDO 2.1 compliant. It supports both the FIDO U2F (Universal 2nd Factor) and FIDO2 protocols, delivering strong two-factor, multi-factor, and passwordless authentication. TokenCore™ Wearable has earned the FIDO Certified label, affirming adherence to FIDO standards.
There are many vulnerabilities and hassles associated with a BYOD approach to MFA via One Time Passwords (OTP) over SMS and authentication apps. These include:
- Mobile phones are vulnerable to SIM Swapping where the attackers trick the phone company into transferring the mobile number to a new SIM card, then the attacked receives all SMS messages, including OTPs.
- SMS is not encrypted end-to-end, which means that messages can be read by cybercriminals while they are in transit.
- Mobile phones get lost and stolen, then attackers have direct access to SMS messages and authentication apps on the stolen device.
- SMS messages can be intercepted in various ways, such as when over un-encrypted or insecure networks allow attackers to read messages.
- Many users inadvertently download malware onto their phone that intercepts SMS messages and forwards them to cybercriminals.
Passkeys are a passwordless authentication method that allows users to verify themselves using their biometric data instead of a password. They were developed by FIDO, of which Token is a member. Passkeys use (PKI) public-key infrastructure just as we do so there is no password to steal.
Major platforms have been working to make passkeys sync securely across devices, which is very convenient for consumers. Apple’s iCloud Keychain and Google Password Manager allow users to access passkeys across multiple devices within their own ecosystems. Token prefers a higher level of security where the user’s private key (these are the keys to the kingdom) never leaves the ring and the ring cannot be accessed via Wi-Fi or cellular signal, and users cannot inadvertently download malware onto their ring, eliminating a major vulnerability.
FIDO (Fast Identity Online) passwordless solutions offer many security benefits by eliminating the use of traditional passwords. This includes:
- Eliminates Password Vulnerabilities
- Resistant to Common Attacks
- Uses Strong Cryptographic Authentication
- Local Device-Based Authentication
- Enhances User Convenience and Security Compliance
- Prevents Account Recovery Exploits
By leveraging FIDO’s passwordless approach, organizations can significantly reduce the risk of security breaches, improve user experience, and comply with evolving security and privacy regulations.
Hardware tokens are great and provide strong security, but
- They frequently get lost.
- They often get left plugged into computers. Leaving a dongle plugged into a device is like leaving your keys in your car when you are away from it.
- They only plug into USB ports [no Bluetooth or NFC support]. TokenCore™ Wearable works via NFC and BLE so it can be used with any device
- They are often not with the user when they need it wherever they are working and with whatever device they are using.
User set up of the ring is easy, intuitive, and takes 10-15 minutes. We have a comprehensive Quick Start Guide to direct users through the process and Token also has a “User Set Up” video, online support resources, and a toll-free number where we support users directly to reduce the burden on your helpdesk.
Because Token Rings are wearables, they are less likely to be lost or stolen. If a user loses a ring, the credentials and biometrics remain safe in the Tamper-Proof Secure Element inside the ring. No one other than the user can ever use the ring or access the protected data stored inside the ring.
Yes, while other major ring makers have a strict No-Exchanges policy, Token allows each ring to be exchanged one time during its life for a different size at no charge. Exchanges are possible beyond the first free exchange for a small charge.