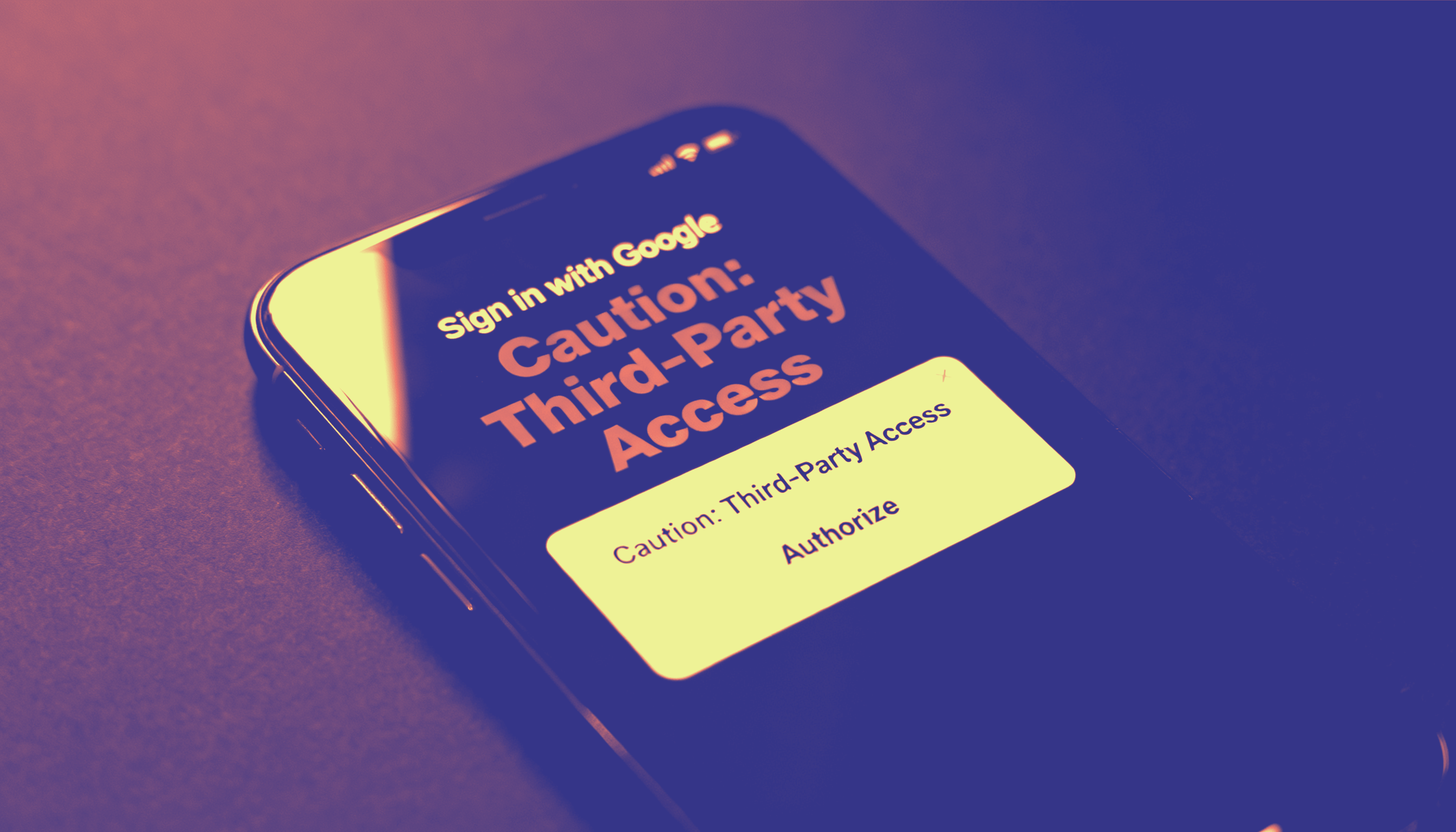
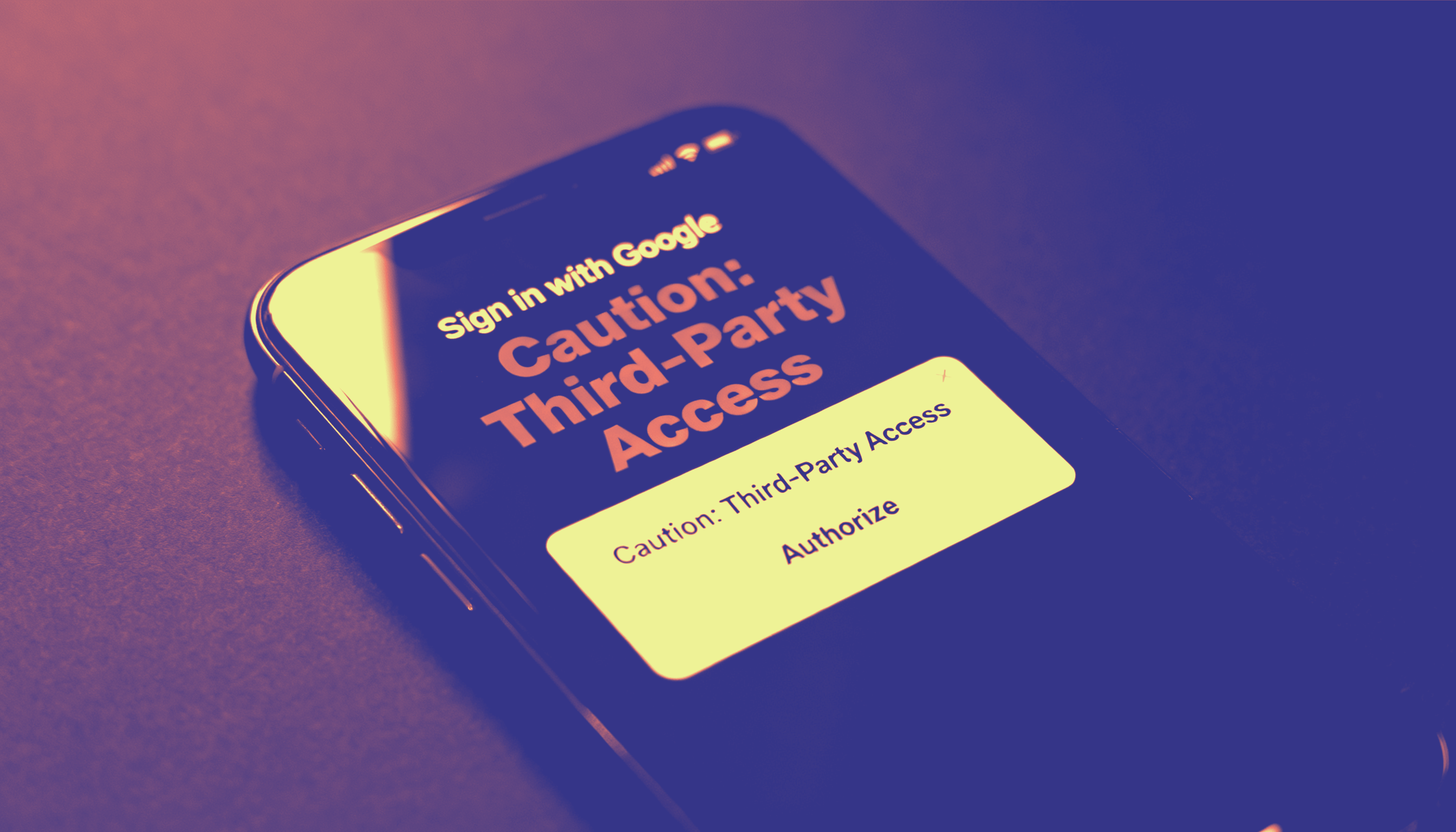
OAuth phishing has fundamentally changed the identity attack surface. It does not defeat MFA — it renders MFA irrelevant.
Classic phishing targets credentials. OAuth phishing targets authorization. Attackers trick users into granting access to a malicious application. The user never enters a password. No MFA prompt appears. The attacker receives a valid OAuth token and gains persistent access — entirely within the normal login flow.
From the user's perspective, the interaction is indistinguishable from a legitimate authorization request. From the defender's perspective, logs show valid OAuth grants, tokens issued by trusted identity providers, and sessions originating from known infrastructure. Nothing triggers an alert because nothing technically went wrong.
MFA Sits Below the Attack
Traditional MFA controls the authentication layer. OAuth operates above it. Once an attacker holds a valid token, MFA has no further role. The attack succeeds not by defeating a control but by bypassing it entirely.
Passkeys face the same structural limitation. Strong authentication at login does not prevent an attacker from abusing delegated authorization after the fact. A token, once issued, can be replayed from any environment. Possession of a token is treated as proof of identity. That equivalence is the vulnerability.
Identity Cannot Be Delegated
Token closes this gap by enforcing something OAuth was never designed to provide: proof that the authorized individual is physically present.
Token binds authentication cryptographically to both the domain and the physical device. Authorization alone does not complete access. Even with a valid OAuth token, access requires a fresh identity assertion — tied to the Token device and confirmed by biometric verification. Identity cannot be delegated. It cannot be replayed.
Because the identity assertion is domain-bound and device-bound, an attacker holding a stolen token cannot produce the cryptographic proof required to complete access. The token exists. The identity does not.
What This Means for Security Leaders
OAuth phishing forces a direct rethink of access models. A log entry that reads "login successful" is no longer assurance of anything. Access that appears legitimate may be adversarial. Security programs built on MFA alone have no visibility into this class of attack.
Token adds a control layer that OAuth cannot bypass — because it anchors access in something OAuth was never designed to verify: the physical presence of a specific, authenticated individual.
OAuth phishing is not an anomaly. It is the predictable outcome of identity systems that separate authorization from identity enforcement. Token reunites those concepts. When identity is cryptographic, biometric, and bound to the individual — possession of a token proves nothing without the person.